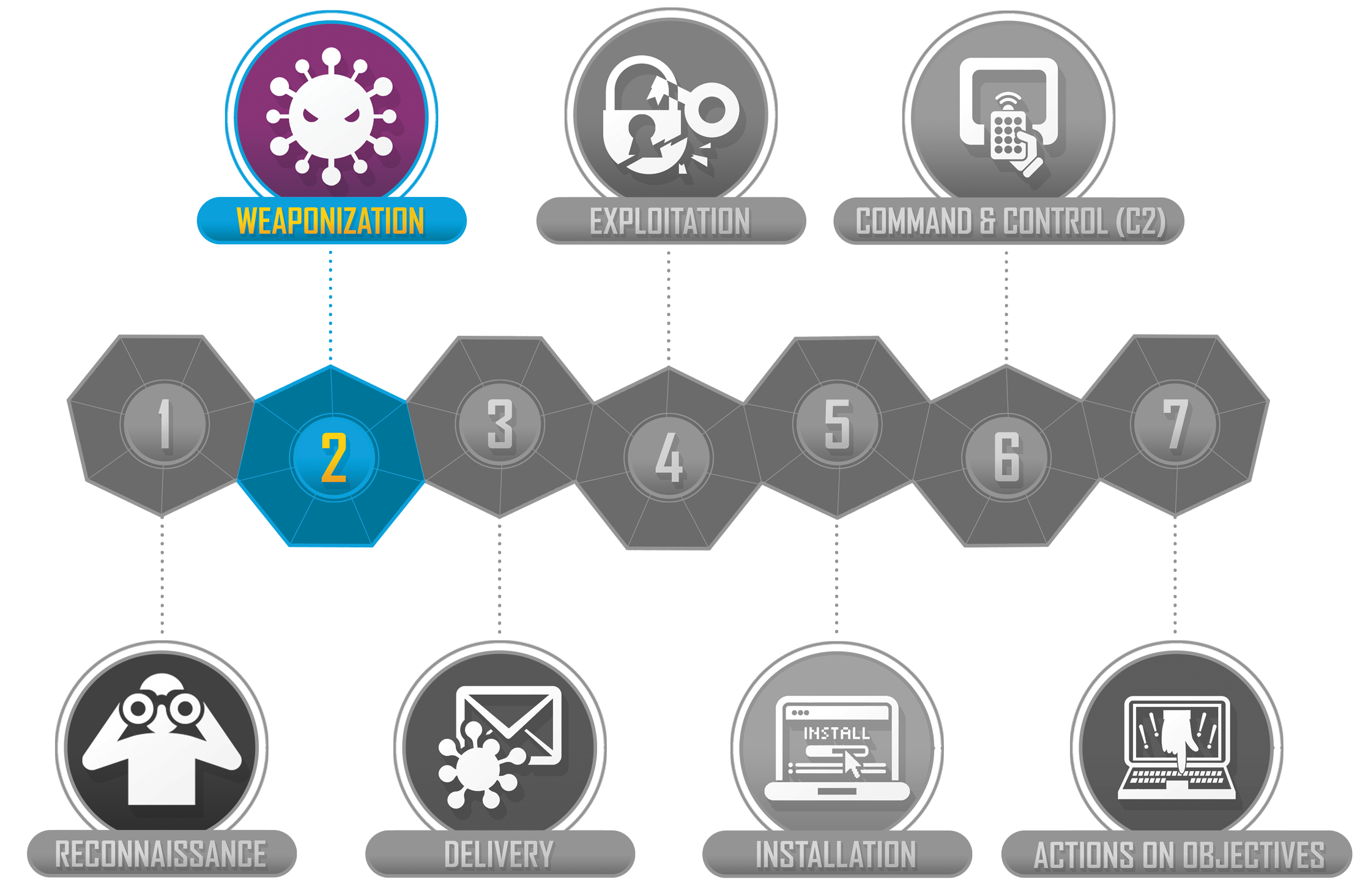
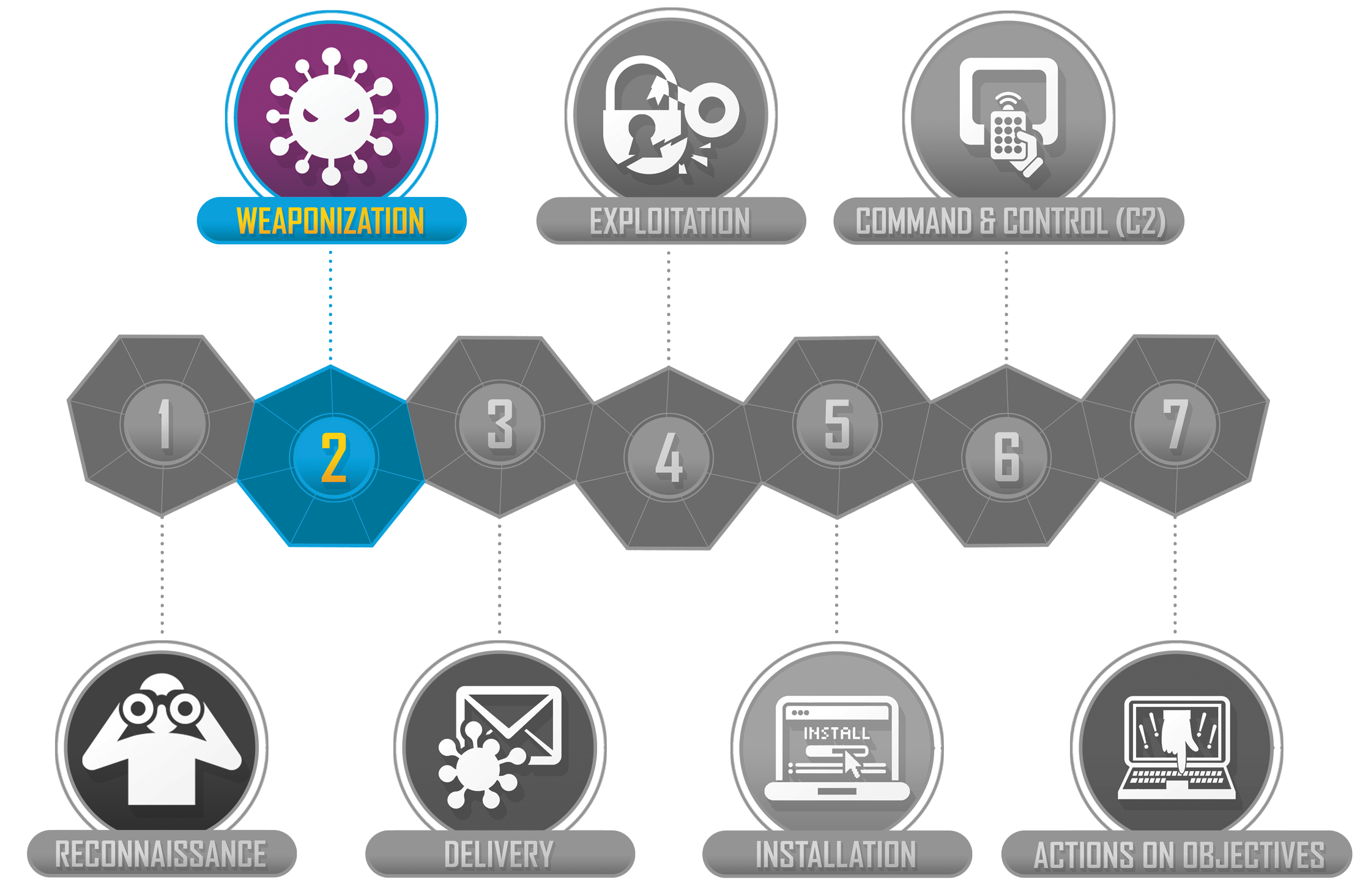
The "Weaponization" is the second step in the Cyber Kill Chain. At this stage, the attacker uses the information obtained in the previous stage to access the tools needed for the attack or develops the tool/script directly. At this stage, preparation for a cyber-attack may differ depending on the sort of attack. For example, if a phishing-type cyber attack is to be carried out, an exploit can be constructed in response to a recognized security vulnerability, or malicious email content can be generated. If the tools for the cyber attack are ready, the attacker completes this phase quickly and moves on to the next phase of the cyber attack. At this point, the attack has not yet commenced, and the victim is generally unaware of the attacker.
The attacker might build many alternative attack techniques or prepare the essential components for a cyber attack during the "Weaponization" process. The following are some of the processes that the attacker might employ at this stage:
It is not possible for SOC analysts and Blueteams to directly prevent the attack preparations of attackers at this stage. However, some measures can be taken, albeit limited. Some of these measures are as follows:
The "Weaponization" step, which is the second step in the Cyber Kill Chain, is explained in this section of the training, along with some of the actions that attackers can take and some measures that Blueteams can take at this stage. In the following section of the training, the "Delivery" step is explained.
Attack Scenario: