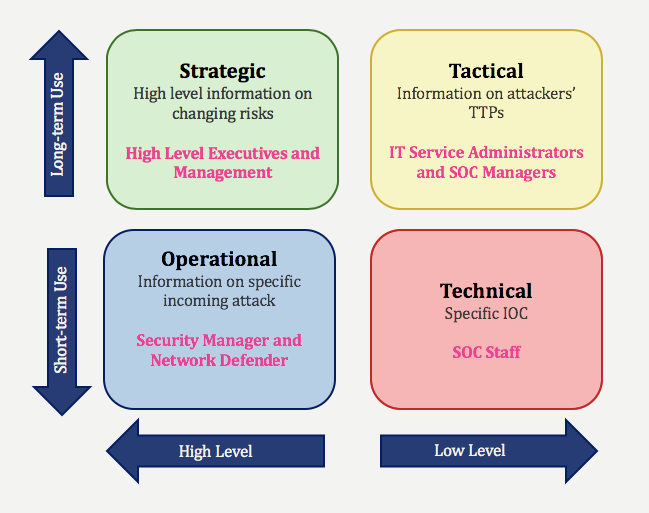
Cyber threat intelligence varies by position within the organization. The intelligence is divided into types since the threat intelligence the technical staff and the manager receive is not the same. The intelligence that the L1 SOC analyst and the SOC manager will receive will differ. This way the intelligence becomes more appealing to its final consumer.
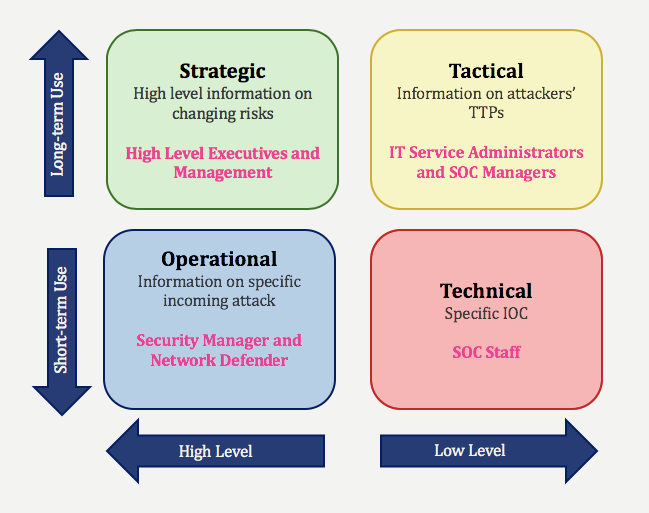
Technical CTI can be considered as the output of more technical analysis studies based on IOCs. It is an output of the technical CTI to create certain rulesets and to protect the organization against attacks by using a report containing hashes of malicious IP addresses, phishing domains, and malicious files, and by investigating the information obtained from this report. This type of intelligence is generally used by the technical personnel (SOC Analyst, Incident Responder) in the organization.
Tactical CTI is used to understand the TTP (Technical, Tactical, Procedure) of the attackers by trying to find answers to certain questions. For instance, we have an intelligence report containing the TTP of an attacker named "mordecai". When we go over this report we should be able to find answers to questions like "what vulnerabilities does the attacker use the most?", "in which countries does the attacker operate?", "what is the attacker's motivation?", and "what methods does the attacker use?" to be able to protect our organization by taking precautionary measures against a possible attack. This intelligence is mostly provided for the management personnel (i.e. SOC Manager, etc.) who are leading the technical teams.
Operational CTI is often confused with Tactical CTI because they have so much in common. Operational CTI also focuses on the attackers' TTPs just like Tactical CTI but it is mostly used for Threat Hunting, unlike tactical CTI. While tactical CTI is a more automated process, operational CTI can focus on a specific type of attack, or a single attacker in particular, and carry out the investigation to a narrower scope. This type of intelligence can be used by Security Managers or Threat hunting personnel in the organization.
Strategic CTI is for the top executives of the organization. It is generally used for long-term tasks such as product purchasing, budgeting, and planning for the organization in the long run by weighing the tactical CTI outputs.