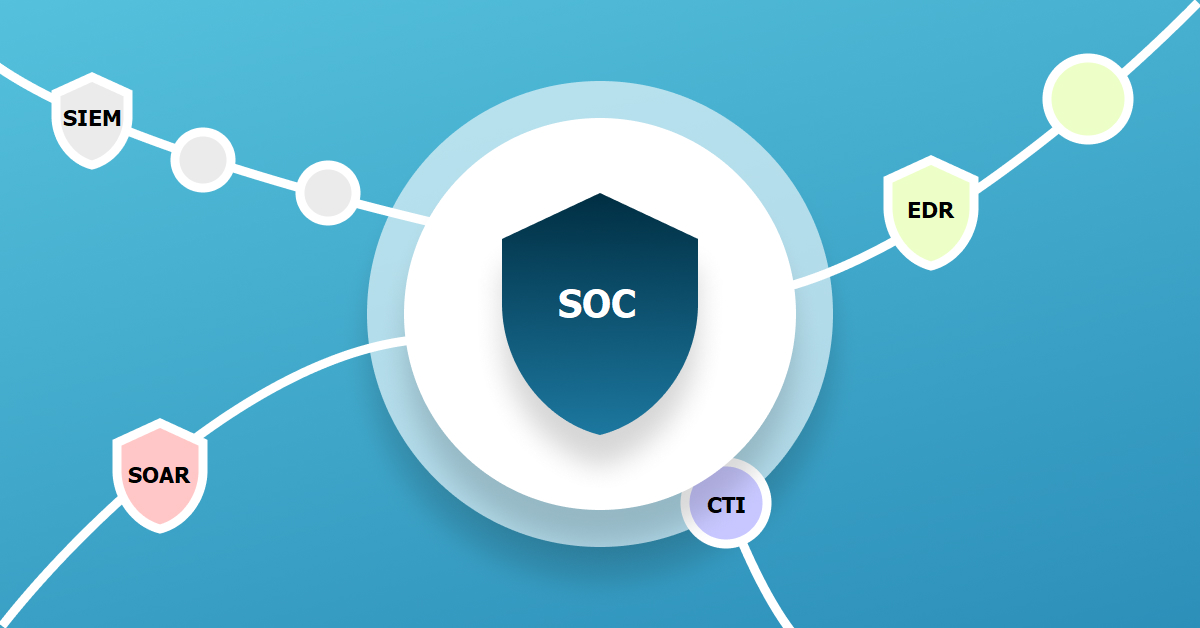
Due to its nature, threat intelligence can be integrated into other SOC products easily. As a result of integration, it is possible to use threat intelligence much more effectively. Organizations generally use products like SIEM, SOAR, EDR, and Firewalls under the umbrella of SOC. Each one of these products has different capabilities in its own use. Combining the outputs of these products in order to gain more effective and functional use will produce the best results for us. In this context, integrating the threat intelligence flow with the security products under the SOC framework will provide us with the highest visibility inside and outside of the organization.
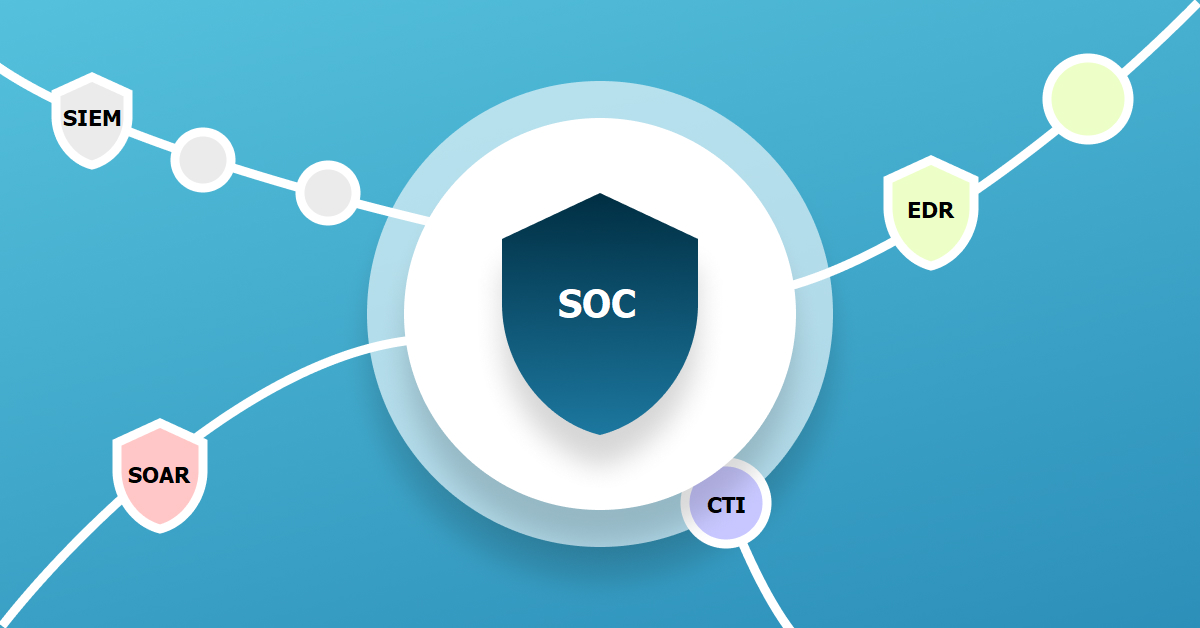
For example, the false information/output on the SIEM side can be minimized if the logs collected in SIEM are integrated with the threat intelligence feed and the necessary elimination of data is set up in accordance with this structure. This will help the SOAR products to produce better quality outputs as we minimized the false information on the SIEM. Integrating threat intelligence with EDR will provide great convenience to detect the risks that will occur on end users' devices. The EDR will make much clear and more detailed detection on the systems if the users' web traffic feeds the threat intelligence. Firewalls are another good example of the SOC and Threat Intelligence integration. if we are able to feed our firewall products, which are used to monitor and manage traffic coming from outside the organization, with threat intelligence, then the Firewalls will be able to take action much faster. If the necessary rules are created for a malicious IP address on it, the firewall will block any traffic that may come from that IP address and the risks will be detected and eliminated right on the spot even before an alert occurs within the SOC security tools.
firewall