Because emails do not necessarily have an authentication mechanism, attackers can send emails in the name of someone else. Attackers can do this by using a technique called spoofing to make the user believe that the incoming email is reliable. Several protocols have been created to prevent the email spoofing technique. The SPF, DKIM, and DMARC protocols can be used to determine whether the sender's address is fake or real. Some email programs check emails automatically. However, the use of these protocols is not mandatory and can cause problems in some cases.
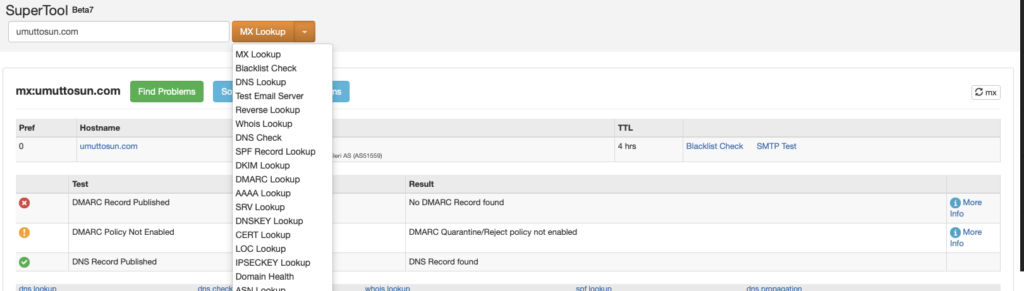
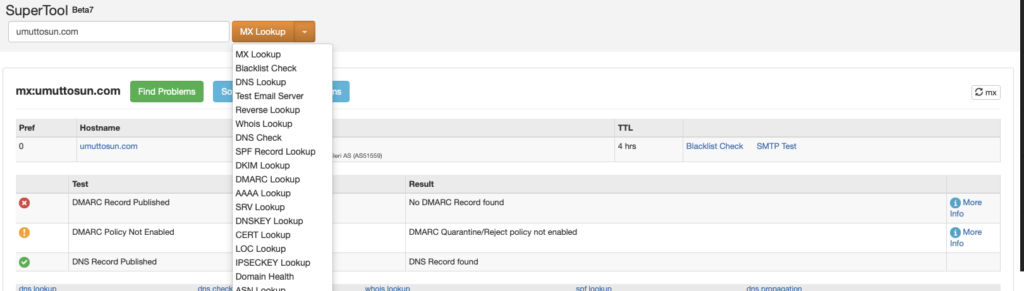
To manually determine if a mail is spoofed or not, the SMTP address of the mail should first be identified. The domain's SPF, DKIM, DMARC, and MX records can be obtained using tools such as Mxtoolbox. Comparing this information will tell you if the email is spoofed or not.
As large institutions using their own mail servers will have their own IP addresses, you can check whether the SMTP address belongs to that minstitution or not by looking at the Whois records of the SMTP IP address.
It is also worth noting that even if the sender's address is not spoofed, we cannot say that the email is safe. Harmful emails can be sent in the name of trusted individuals by hacking corporate/personal email addresses. Such cyber-attacks have happened in the past, so it is always worth considering the possibility.
Many parameters are needed to analyze a phishing attack. The following parameters can give us an idea of the size of the attack and the target audience if we perform a search on the mail gateway.
In addition to the email numbers, it is necessary to know the recipients' addresses and time information in the search results. If malicious emails are constantly being forwarded to the same users, their email addresses may have somehow been leaked and shared on sites such as PasteBin.
Attackers can find email addresses using the Harvester tool on Kali Linux. Posting personal email addresses on websites could provide a potential attack vector for attackers, so it is recommended that such information is not explicitly shared.
If the emails are sent out of office hours, the attacker may be in a different time zone. By gathering this sort of information, you can begin to figure out the nature of the attack.
Because emails do not necessarily have an authentication mechanism, attackers can send emails in the name of someone else. Attackers can do this by using a technique called spoofing to make the user believe that the incoming email is reliable. Several protocols have been created to prevent the email spoofing technique. The SPF, DKIM, and DMARC protocols can be used to determine whether the sender's address is fake or real. Some email programs check emails automatically. However, the use of these protocols is not mandatory and can cause problems in some cases.