Advanced Persistent Threat (APT) Groups, are the hacker groups that may include many different people and groups that carry out cyber attacks in a targeted and systematic way, with governments support from time to time. APT groups may conduct cyber attacks with different motivations. For example, the group may have a specific mission, may be conducting their attacks for money, or may be foreign government supported and conduct their attacks to obtain their national ideals.
Within the MITRE ATT&CK Framework, information about APT groups is collected which helps identify which APT group is targeting which systems and which cyber attack techniques are being implemented. When all this information is gathered together and evaluated with the MITRE ATT&CK matrix, the attack map of the APT group can be revealed.
Groups: 135
You can check the below link to see the updated number:
Groups: https://attack.mitre.org/groups/
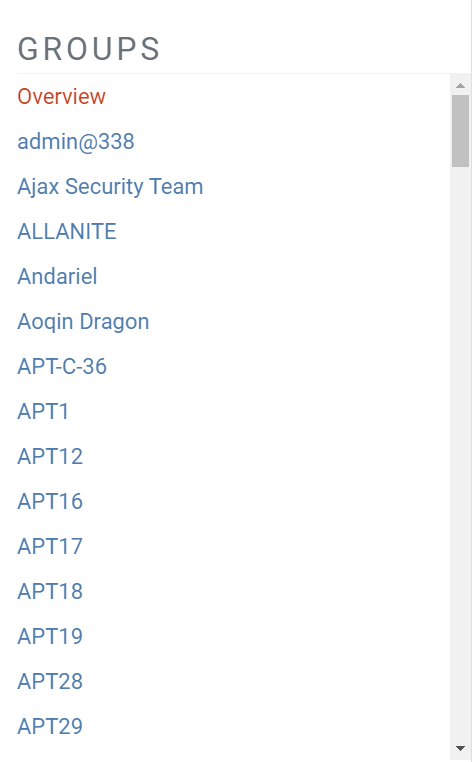
When the above site is visited, a menu like the image below will appear on the left side of the page:
(Image Source: mitre.org)
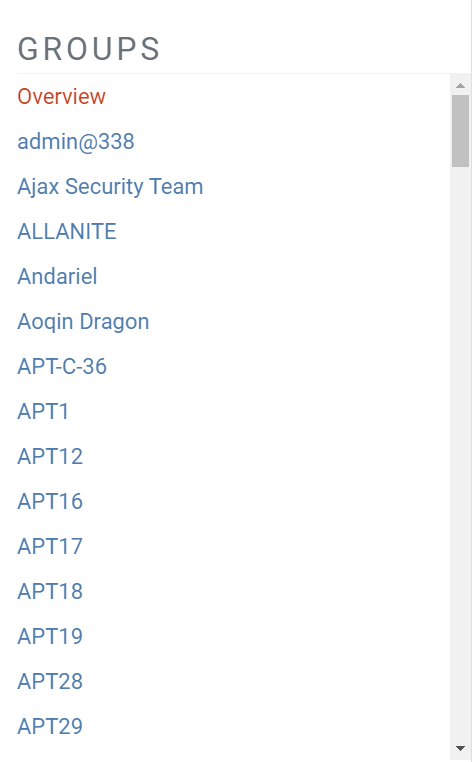
Using this menu, information about the listed APT groups can be accessed. For example, the information about the “Lazarus Group” APT group is as follows:
(Image Source: mitre.org)
As seen in the image above, each APT group listed in the MITRE ATT&CK Framework has a unique Group ID, Name and Description.
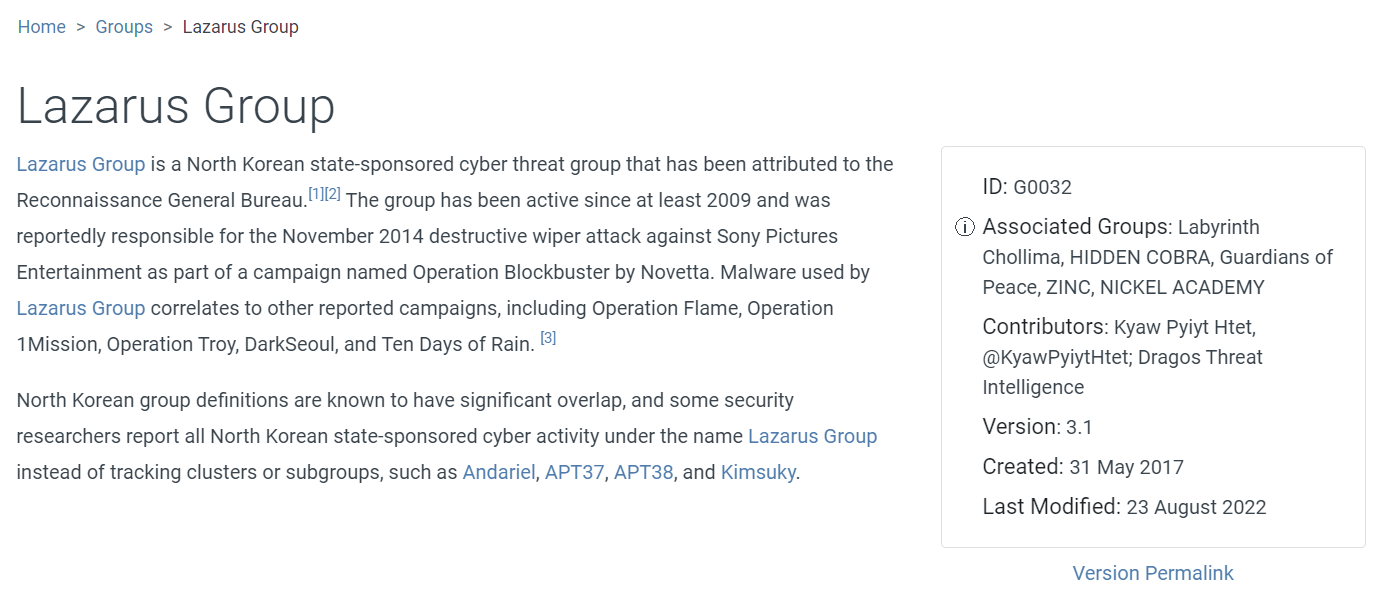
You can also see the information about the techniques used by the group in cyber attacks at the bottom of the page:
(Image Source: mitre.org)
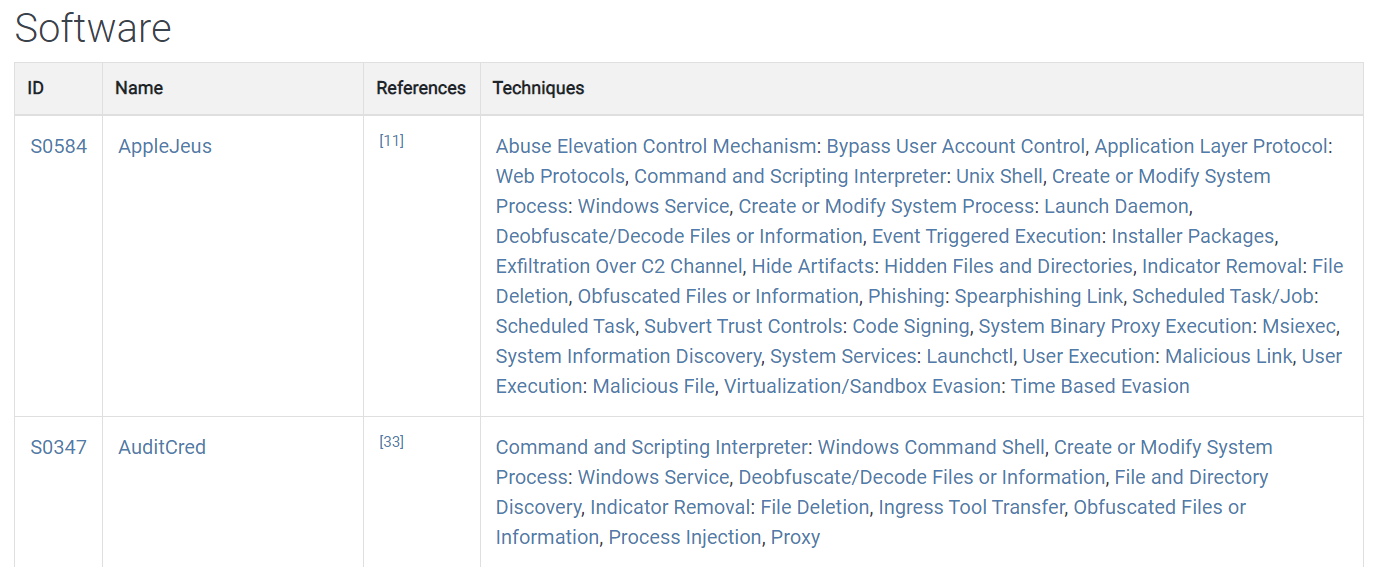
Under the “Techniques” column, you can see what tools, software or techniques that the APT group was leveraged for the attack. For example, some software used by the “Lazarus Group” APT group is as in the image below:
(Image Source: mitre.org)
We have covered the Groups included in the MITRE ATT&CK Framework in this part of the training. We will detail the “Software” topic in the next part of the training.