In this lesson, we will perform an Endpoint Security analysis, which involves examining the processes and browser activity on the affected endpoints to identify any further indicators of compromise.
Endpoint security operates as an Endpoint Detection and Response (EDR) system, collecting log data and providing insight into activity on the host machine. Like EDRs such as Carbon Black, SentinelOne, CrowdStrike, and most others EDRs, LetsDefend Endpoint Security allows you to connect to machines, collect detailed logs, and even isolate compromised machines.
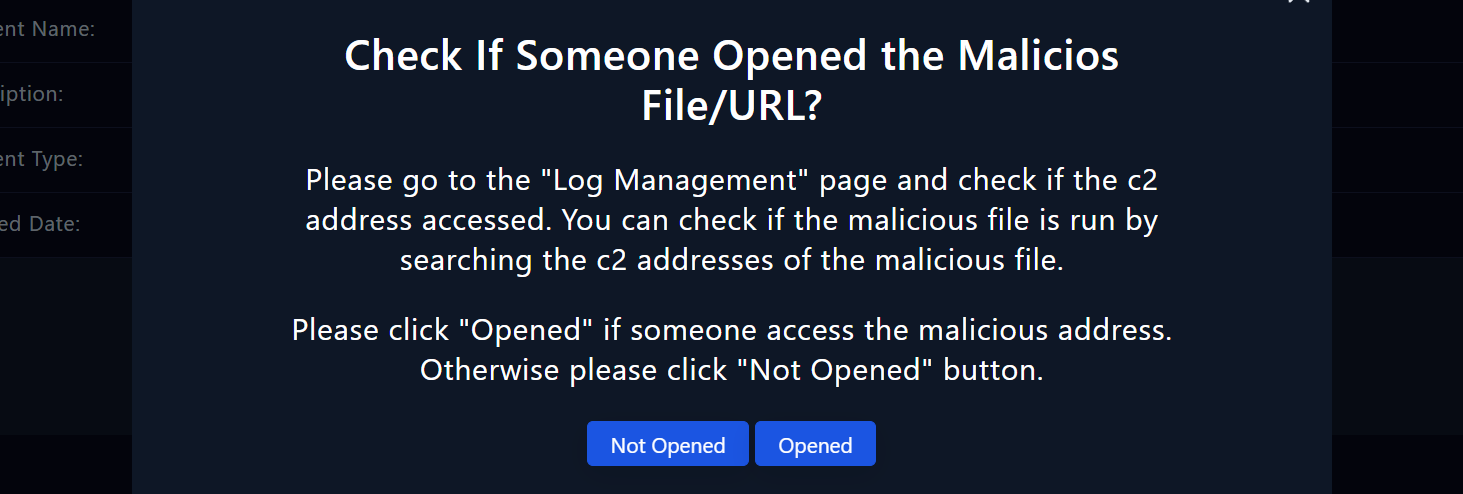
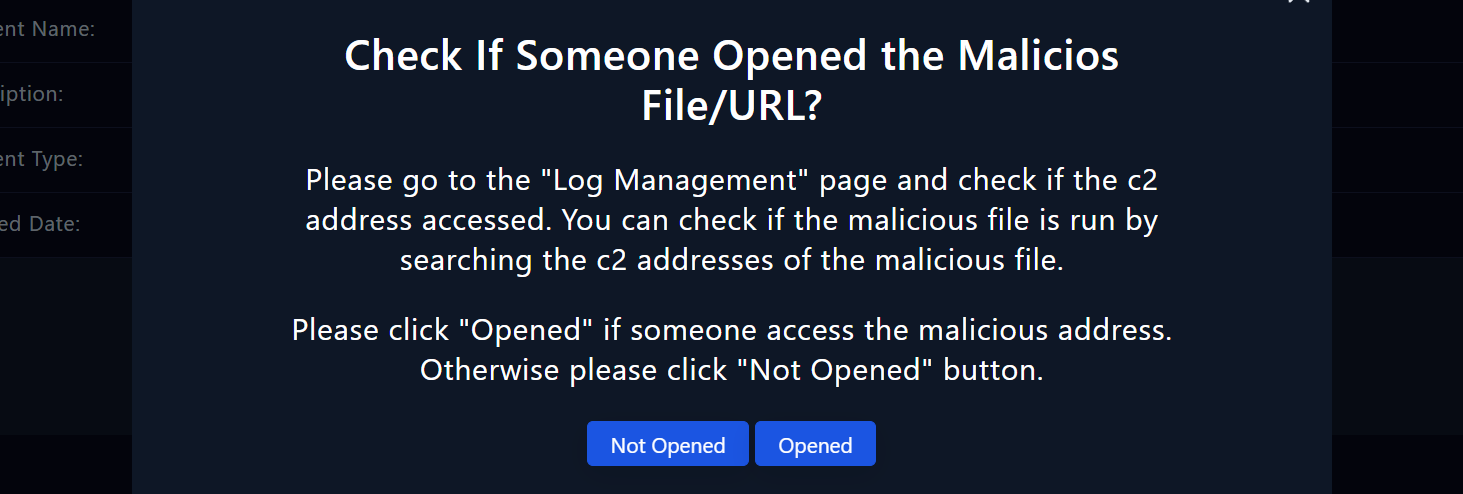
We will continue to examine the actions taken by the malware on Endpoint Security in more detail. This approach will allow us to verify whether the malware was executed on the system and identify the processes or commands it executed.
To begin the analysis, navigate to Endpoint Security. This section provides comprehensive details about the host machine, including its processes, network actions, terminal history, and browser history.
Steps to Follow:
Select the Host:
Process and network action analysis aims to detect suspicious processes and identify communication with command and control addresses.
Analyze Processes: