.png)
Open redirection is a web security vulnerability that occurs when a website or web application redirects users to a different URL without proper validation or sanitization of the target URL. Attackers can exploit Open Redirection to trick users into visiting malicious websites or performing actions unintended by the website owner.
In an open redirection attack, an attacker typically crafts a legitimate URL hosted on the vulnerable website, but includes a malicious URL as a parameter or query string. When a user clicks on the crafted URL, the website's redirect mechanism automatically redirects the user to the malicious URL, which can lead to various malicious activities, such as phishing attacks, spreading malware, or stealing sensitive information.
Open redirection vulnerabilities commonly occur when websites use user-supplied input, such as URLs, as part of their redirect mechanism without proper validation or sanitization. To prevent open redirection attacks, web developers should validate and sanitize all user-supplied input used in redirections, and ensure that only trusted and whitelisted URLs are allowed for redirection. Additionally, it's important to implement proper authentication and authorization mechanisms to ensure that only authenticated and authorized users can perform redirects. Regular security testing, including vulnerability scanning and penetration testing, can also help identify and fix open redirection vulnerabilities in web applications.
There are several types of open redirection vulnerabilities that can occur in web applications. These include:
It's important for web developers to be aware of these different types of open redirection vulnerabilities and implement proper validation and sanitization of user-supplied input to prevent such vulnerabilities in their web applications.
Here's an example of a vulnerable code in a web application that demonstrates an open redirection vulnerability using PHP:
.png)
In this example, the web application takes a target URL as a query parameter (\url\\\\) from the user and uses it in a redirect without validating or sanitizing the input. This can lead to an open redirection vulnerability, as an attacker can craft a malicious URL and pass it as the \url\\\\ parameter, leading to unintended redirection to a malicious website.
For example, an attacker could create a URL like this:
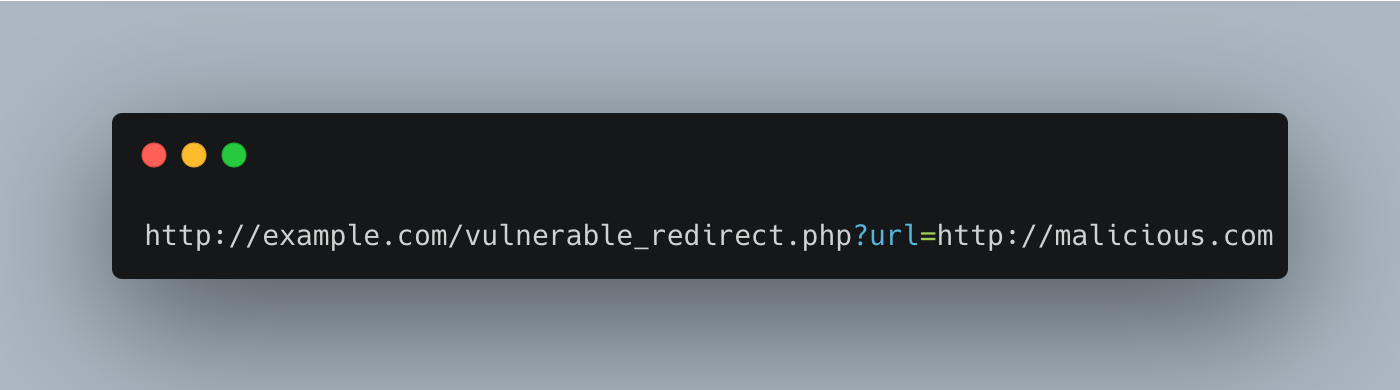
When a user clicks on this URL, the vulnerable application will automatically redirect the user to \http://malicious.com\\\\, which could be a phishing website or a site hosting malware.