Command injection attacks are attacks that occur when data received from a user is not sanitized and is passed directly to the operating system shell.
Attackers exploit command injection vulnerabilities to execute commands directly on the operating system. Since the attacker's priority is to take control of the system, these vulnerabilities are more critical than other vulnerabilities.
A misconfigured web application would grant the attacker access with admin rights because the command the attacker sends uses the rights of the web application user.
Command injection vulnerabilities occur when the data received from the user is not sanitized. Let's examine command injection vulnerabilities with an example.
Suppose we have a basic web application that copies the user's file to the "/tmp" folder. The web application code is shown below:
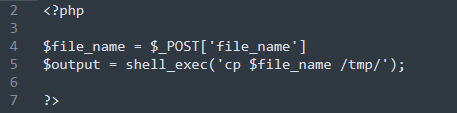
Under normal circumstances, if used correctly, the application will work normally. For example, if we upload a file called "letsdefend.txt", it will successfully copy the file to the "/tmp" folder.
So what if we upload a file called "letsdefend;ls;.txt"? The command would be:
Command: cp letsdefend;ls;.txt
The ";" indicates that the command has ended. So if we look at the payload above, there are three different commands that the operating system executes. These are:
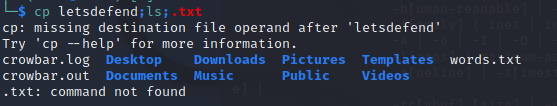
The first command is for the copying process, but if the parameters are not entered correctly it will not work correctly.
Command #2 is the directory listing command that the attacker wants to execute. The user does not receive the command output, so the attacker cannot see the files in the directory, but the operating system successfully executes the command.
If the operating system tries to run command number 3, it will get an error message because there is no ".txt" command.