Brute forcing is a type of attack that involves attempting to guess a password or authentication token by systematically trying every possible combination of characters until the correct one is found. In the context of web attacks, brute forcing typically refers to the process of using automated tools to repeatedly submit login requests to a web application using different username and password combinations until a valid one is discovered.
Brute force attacks can be used to gain unauthorized access to a system, steal sensitive information, or launch further attacks against the target or other systems. They can be particularly effective against weak or poorly protected passwords, but can also be very time-consuming and resource-intensive for the attacker, especially if the target system has implemented measures to detect and block brute force attacks.
Brute force attacks are one of the simplest and most straightforward methods of attacking a web application, and it works by systematically trying every possible combination of usernames and passwords until the correct one is found. This process is typically automated using specialized software or scripts, which can try thousands or even millions of combinations per second.
The basic idea behind a brute force attack is to exploit the weak or easily guessable passwords that a lot of people use especially the non-techy users, such as common dictionary words, simple number sequences, or their own names or birthdates. By systematically trying every possible combination of characters, attackers can eventually find the correct password and gain access to the target system.
Brute forcing on web applications is a common attack vector used by hackers to gain unauthorized access to user accounts or web servers. In this type of attack, the attacker will use automated tools to submit multiple login requests to the targeted web application using different usernames and passwords, in an attempt to find the correct credentials and gain access to the system.
Web applications are particularly vulnerable to brute force attacks because they are often accessible over the internet and rely on user authentication to control access to sensitive data or functionality. If an attacker is able to guess a valid username and password, they can potentially gain access to sensitive user data, such as financial information, personal data, or confidential business information.
Actually, it's not just guessing usernames and passwords also, directory brute forcing on web applications is another type of brute force attack that involves guessing file or directory names on a web server in order to find hidden or sensitive files or directories. In this type of attack, the attacker will use automated tools to submit requests to the targeted web server using different file or directory names, in an attempt to find files or directories that are not meant to be publicly accessible.
This type of attack can be effective against web applications that do not implement proper access controls or that have poorly configured web servers. To prevent directory brute force attacks, web application developers can implement access controls to restrict access to sensitive files and directories, and can configure their web servers to block requests for known sensitive files and directories.
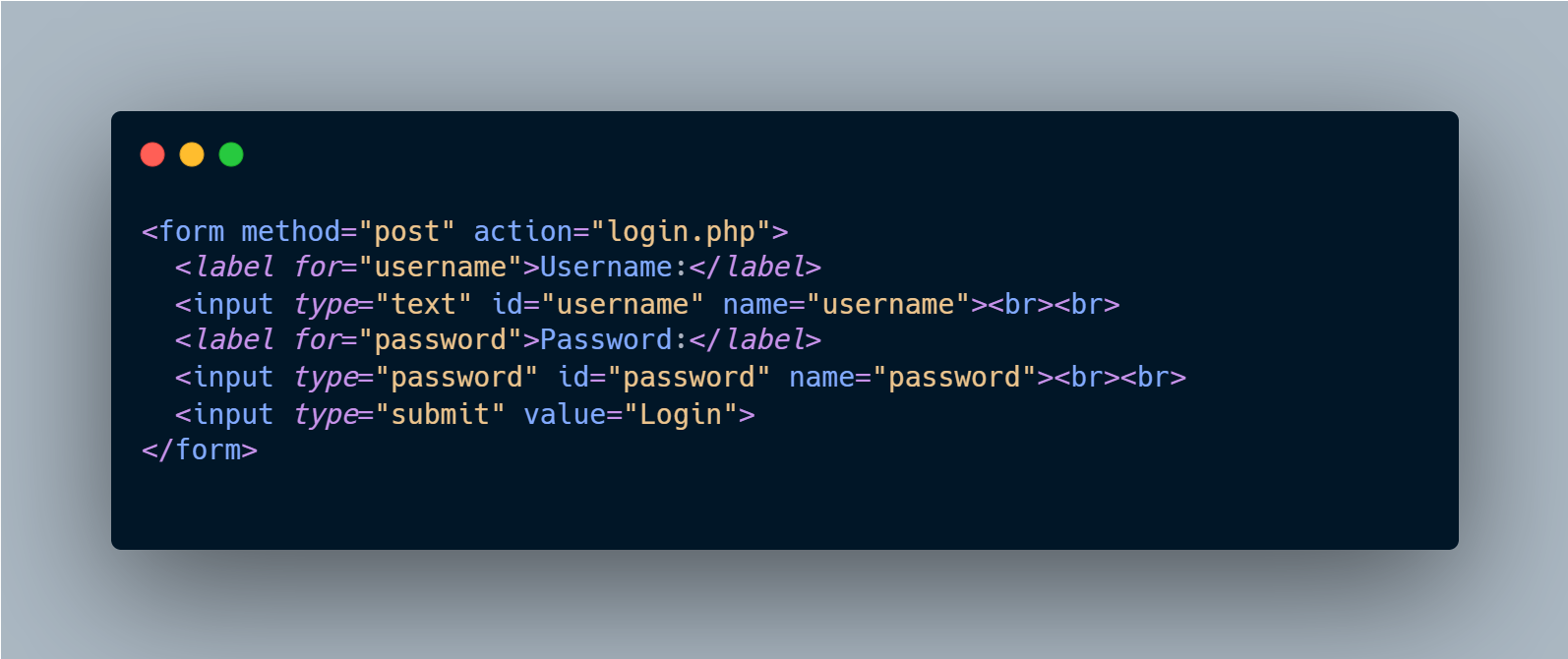
Here's an example of vulnerable code that is susceptible to Brute Forcing attacks in a PHP script:
This form is vulnerable to brute force attacks because it allows unlimited login attempts and does not implement any security measures to prevent automated login attempts.
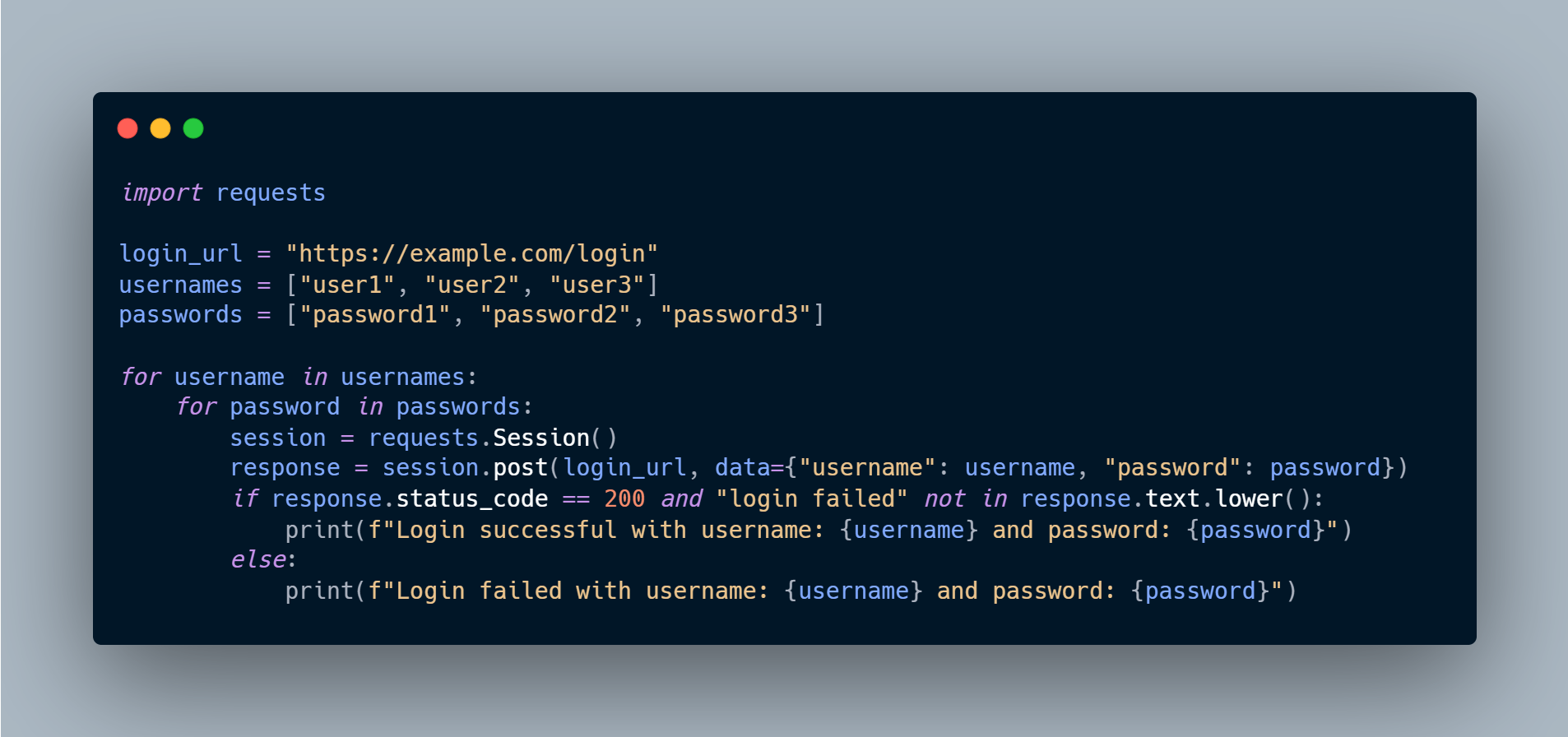
Here's an example of how you can use Python requests library to send multiple login requests with a list of usernames and passwords:
Brute forcing can have significant impacts on a target system or application. Here are some of the potential impacts of brute forcing: